Oxar Ransomware – A Rising Data Encryption Threat
Oxar ransomware is an advanced and particularly harmful file encrypting cryptovirus that belongs to ransomware family, which infiltrate the user’s system and encrypt (lock) every single data available on the hard drive and locks down the entire system.
Oxar Ransomware is categorized as dangerous malware because the infection can have severe outcomes, and capable to infect almost all Windows Operating System version like Windows XP, Windows7, Windows8, Windows8.1 and Windows 10.
It is developed by the team of cyber attackers with the sole intention to extract huge ransom money by phishing innocent users.
If your computer has just become a victim of such an attack, you’re probably wondering how to deal with it and how to decrypt .oxr files without paying the ransom requested by the hackers.
However, since you are on this page, you are already a step ahead and have a chance to protect your PC from .oxr files virus before it causes more harm to your valuable data.
As the article advances, you will come to know how the ransomware infected your system and how to remove Oxar OXR ransomware easily without paying the ransom.
Followed by various removal techniques which encapsulate manual preventive methods and a robust Oxar ransomware removal tool which will help to safeguard your PC.
What is Oxar ransomware?
Oxar ransomware encrypts files and deletes system’s backup with the help of sophisticated cipher algorithm and compels you to pay money for your files within some time limit.
.Oxar files virus belong to one of the worst computer threat currently, it gets into your system through tricky ways, such as spam emails, third-party websites, torrents, and peer-to-peer file sharing, freeware (fake software updates), fake download portals, and social clickjacking etc.
The Oxar ransomware will encrypt all kinds of files and folders stored in your computer including texts, music, images, documents, pdf, backup files, etc.
Instead of directly locking files, it changes the encrypted file names by appending OXR extension to the file name.
For example, an image named test.jpg will be encoded and renamed to test.OXR.
Whenever a user attempts to open a locked file, it displays a ransom message informing victims of the encryption and giving instructions regarding the method to pay ransom money in Bitcoin or other cryptocurrencies.
Even if the victim contacts the hacker and pays the ransom, it is tough to crack Oxar ransomware AES/DES cryptography technique that generates unique decryption keys, which means using any other keys does not give you the desired result. Besides, they store them in remote servers and are the only ones who can access them.
It is recommended that you should never believe such cybercriminals because once payment is submitted, there is no such guarantee that you would be able to recover encoded files.
Thinking of Paying the Ransom? Stop Thinking; Always Say NO To Cyber-Criminals!
Despite the fact that we highly advise not paying the ransom, we understand that a few organizations would not have the capacity or technical guidance to get away without the information that has been put away on the encrypted systems, so unfortunately in such cases, paying the money will be the only option to advance the business.
Cybersecurity specialists never recommend you to pay! Paying ransom is not a good option because once you start paying a ransom, the cyber attackers will demand more.
We advise investing the money you are demanded to pay into some backup may be a better option because data loss wouldn’t be a problem.
Remember that you can never be sure whether the criminals would give you a working decrypting key.
Further, cyber attackers via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information, and ATM Card information.
This personal data, later, may be sold to third parties which can lead to serious privacy violations, financial loss or even theft.
Thus, we recommend using a reliable, robust anti-malware removal tool such as Malware Crusher which will help you to remove Oxar ransomware or other malicious content, saving you the time and struggle of hunting down several malicious files.

How to prevent Oxar ransomware from entering in computer
There have been instances in the past showing the users were hit by the same ransomware for the second time, even though they have already paid the ransom amount.
From here, all we can say is if you don’t act quickly in the right way, you might not get another chance, so we suggest you follow removal guide to delete Oxar ransomware that may also help you in the removal process of other malicious content. The guide is divided into two parts:
- Unlock Computer In Safe Mode
- Restore System
Temporarily Disable Oxar ransomware in safe mode using Command Prompt
1. Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start > then shut down > then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
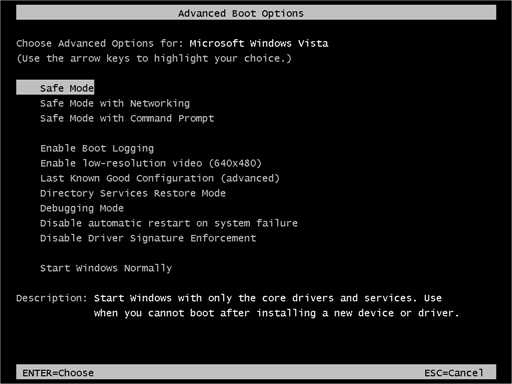
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
2. Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
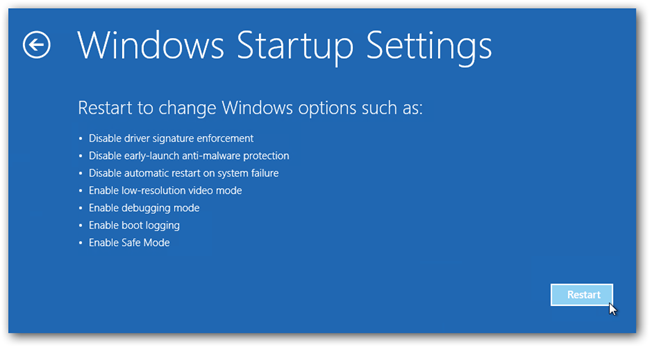
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then start-up settings and finally press restart.
- Once your computer restarts and gives you the list of start-up options you need to select Enable Safe Mode with Command prompt.
3. Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
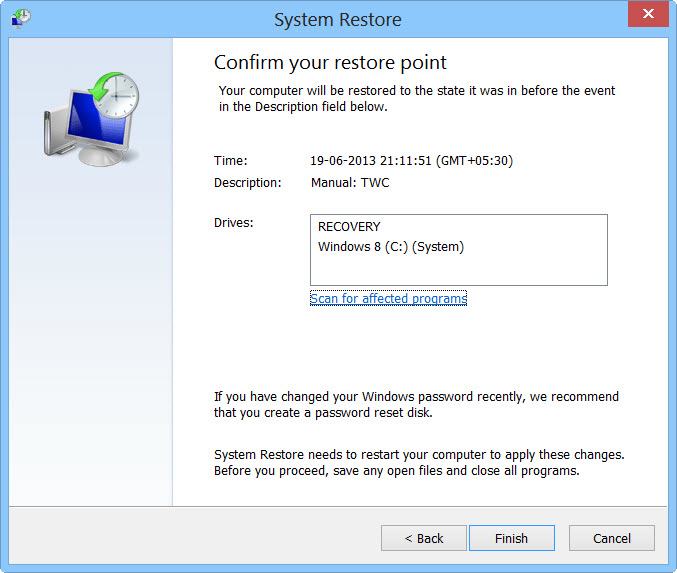
- Then, click next followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you make a copy of backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as pen drive, CD or DVD.
While installing Windows, allocates disk space to C, D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete; also your data is backed up. Now you must create a strong firewall against such intrusions and prevent them in the future.
Nowadays, cyber attackers have learned to make their malware more adaptable, resilient and more damaging. Common antivirus software cannot protect you from all cyber threats at the same time.
Though, we need to comprehensively upgrade our cyber defense systems and processes to more effectively guard against cybersecurity risks, as well as to respond in a timely and robust manner to prevent any intrusion in the future.

Note* - We recommend ITL Total Security and Malware crusher, among the best reputed anti-malware software which will help you to block viruses, adware and other malware on your PC. It consists of several features to protect your system from damage and keep you safe always. They are fully loaded with certain useful features like Real-Time Protection, Web Protection, Live updates, and many more.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
